The underground economy of stolen financial data has grown significantly over the past decade. Cybercriminal networks operate bclub hidden marketplaces where compromised payment information is bought and sold. Among the most commonly traded items in these illegal markets are credit card dumps and CVV2 data.
While these terms are frequently discussed in cybersecurity circles, many people are unfamiliar with what they actually mean and how they impact businesses and consumers. Understanding how these markets operate is important for improving digital security and preventing financial fraud.
This article explores what card dumps and CVV2 data are, how cybercriminals obtain them, and what individuals and organizations can do to protect themselves.
What Are Credit Card Dumps?
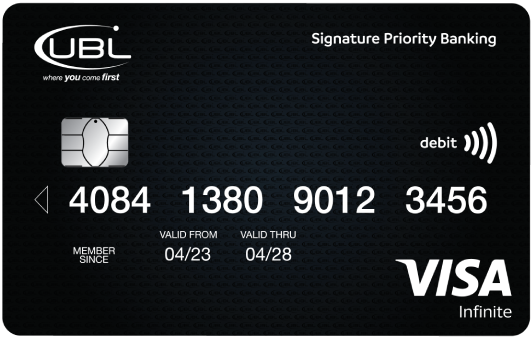
A credit card dump refers to the data stored on the magnetic stripe of a payment card. This information includes:
- Card number
- Cardholder name
- Expiration date
- Service code
- Other encoded information used during transactions
When criminals obtain this data, they can sometimes clone the information onto another magnetic stripe card. This cloned card may then be used for fraudulent transactions in places where magnetic stripe authentication is still accepted.
Although many regions have adopted EMV chip technology, magnetic stripe data still exists and can be exploited in certain payment environments.
What Is CVV2 Data?
The CVV2 (Card Verification Value) is the three or fourdigit security code printed on payment cards. This code is typically required when making online or cardnotpresent transactions.
When criminals obtain CVV2 information along with other card details, they may attempt fraudulent purchases on ecommerce websites. Because online payments rely on card numbers, expiration dates, and security codes, stolen CVV2 data can enable unauthorized transactions.
For this reason, protecting CVV2 information is critical for both consumers and merchants.
How Card Data Is Stolen
Cybercriminals use several methods to obtain card information. Some of the most common techniques include:
1. Data Breaches
Largescale data breaches occur when hackers infiltrate company systems and extract stored customer information. Retailers, payment processors, and online services may become targets if their security systems are weak.
When breaches occur, thousands or even millions of payment records may be exposed.
2. PointofSale Malware
Pointofsale (POS) malware infects payment terminals or retail systems. The malware captures card data during transactions and sends it to attackers.
Several highprofile breaches in the past were caused by POS malware collecting magnetic stripe information from retail networks.
3. Phishing Attacks
Phishing attacks trick users into revealing sensitive financial information through fake emails, websites, or messages. Victims may unknowingly provide card details on fraudulent websites that appear legitimate.
4. Skimming Devices
Skimming devices are small hardware tools placed on card readers such as ATMs or fuel pumps. These devices capture magnetic stripe data when a card is swiped.
Some advanced skimming setups also include hidden cameras or keypad overlays to capture PIN numbers.
5. Malware on Personal Devices
Malicious software installed on computers or smartphones may intercept payment data entered during online purchases. This information can then be transmitted to cybercriminal networks.
The Structure of Underground Carding Markets
Cybercrime marketplaces operate similarly to legitimate ecommerce platforms, but they function in hidden parts of the internet. These platforms often include:
- Vendor listings
- Reputation systems
- Escrow services
- Cryptocurrency payment methods
Vendors may advertise different types of stolen data, categorized by factors such as geographic origin, issuing bank, or card type.
Although these markets constantly change and disappear due to law enforcement actions, new ones frequently emerge.
Why Stolen Card Data Is Valuable
Stolen payment information has financial value because it can be used to conduct fraudulent purchases or resold multiple times within criminal networks.
Several factors influence the value of stolen card data, including:
- Card type (credit vs debit)
- Country of origin
- Spending limit
- Associated personal information
Cards linked to high spending limits or wealthy regions often attract higher prices in underground markets.
Impact on Businesses and Consumers
The trade of stolen card data affects both individuals and organizations.
Consumer Impact
Victims of card fraud may experience:
- Unauthorized transactions
- Account disruptions
- Temporary financial losses
- Stress and identity theft concerns
Although banks often bclub.tk reimburse fraudulent charges, the process can still be disruptive.
Business Impact
Companies that experience data breaches face serious consequences, including:
- Financial penalties
- Loss of customer trust
- Legal liabilities
- Expensive security upgrades
Reputation damage alone can take years to repair after a major breach.
How Consumers Can Protect Their Card Data
Individuals can take several steps to reduce the risk of card fraud:
Monitor financial statements regularly
Review bank and card statements to identify suspicious activity early.
Use secure payment methods
Digital wallets and tokenized payment systems reduce exposure of real card numbers.
Enable transaction alerts
Many banks provide realtime notifications for purchases or withdrawals.
Avoid entering card data on suspicious websites
Always verify that websites use HTTPS and belong to legitimate businesses.
Use strong passwords and twofactor authentication
This helps protect online accounts linked to payment information.
How Businesses Can Strengthen Payment Security
Organizations must also implement strong security measures to protect customer data.
Adopt PCI DSS compliance
The Payment Card Industry Data Security Standard provides guidelines for protecting cardholder information.
Use tokenization and encryption
Sensitive payment data should never be stored in plain text.
Regularly update systems and software
Security patches help prevent exploitation of known vulnerabilities.
Implement network monitoring
Continuous monitoring helps detect suspicious activity quickly.
Train employees on cybersecurity awareness
Human error remains one of the biggest causes of security breaches.
The Role of Law Enforcement and Cybersecurity Experts
International law enforcement agencies actively investigate cybercrime networks involved in payment fraud. Over the years, several large underground marketplaces have been shut down through coordinated operations.
Cybersecurity researchers also play an important role by:
- Tracking emerging threats
- Reporting vulnerabilities
- Helping organizations improve defenses
Despite these efforts, cybercrime continues to evolve, making cybersecurity awareness more important than ever.
Conclusion
The illegal trade of credit card dumps and CVV2 data represents a major challenge in the digital economy. Cybercriminal groups constantly develop new methods to steal and exploit financial information, targeting both consumers and businesses.
Understanding how stolen card data is obtained and distributed helps individuals recognize the risks and take preventive measures. Strong cybersecurity practices, combined with vigilant monitoring and improved payment technologies, are essential in reducing financial fraud.